Every MCP server scanned.
Every threat surfaced.
Automated CVE detection, 5 of 10 OWASP MCP checks, tool poisoning detection, and auth gap analysis across your entire MCP fleet. One command. Plugs into CI/CD with --ci flag.
In action
One command. Full fleet scan.
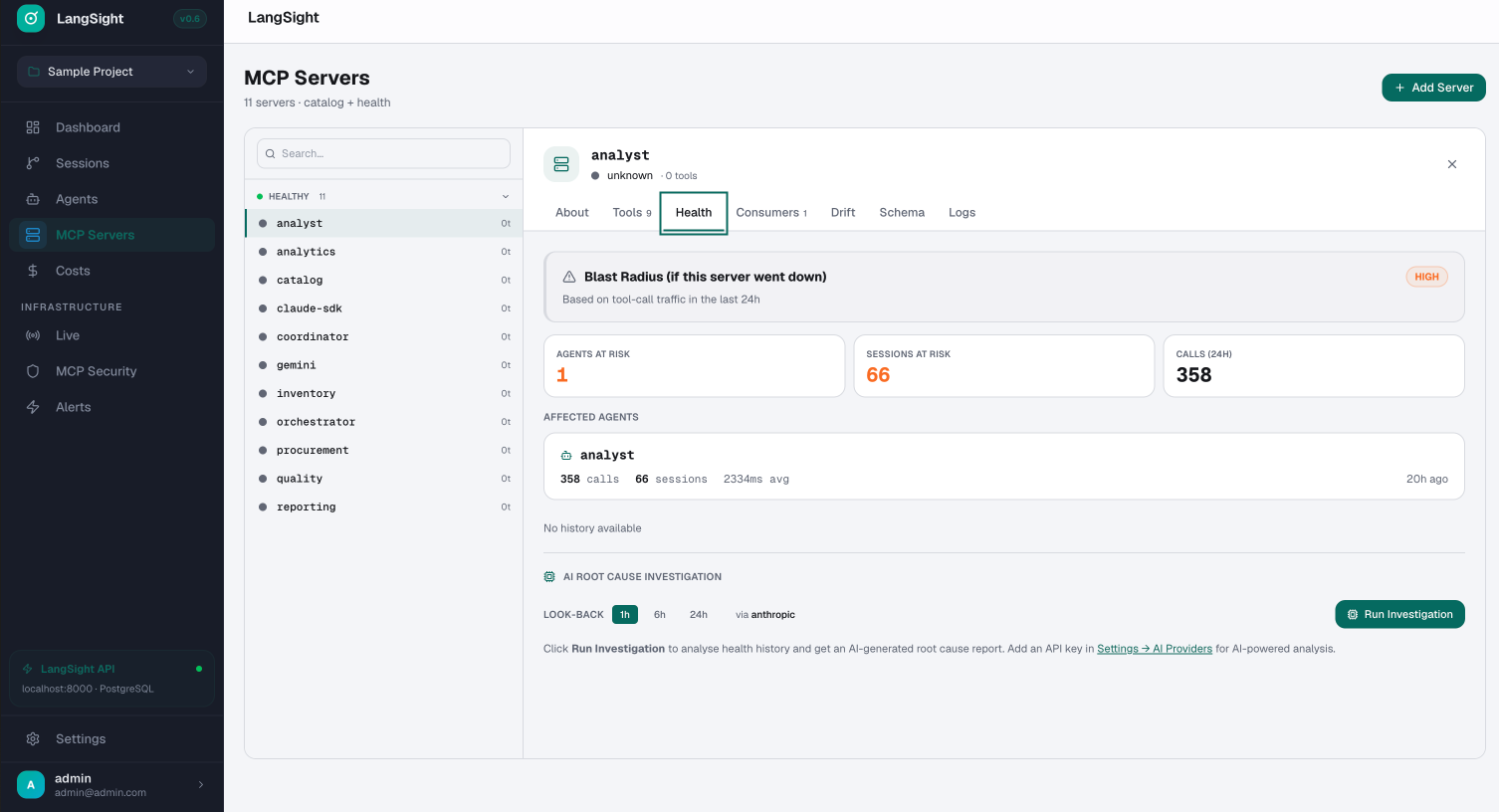
Dashboard
Blast radius + AI root cause
built into every server panel.
OWASP MCP Top 10
5 of 10 checks automated. More coming.
The OWASP MCP Top 10 was published in 2025 after real CVEs and tool poisoning attacks emerged in production. LangSight automates 5 checks today; the rest are in progress.
Tool poisoning detection
Injected instructions.
Hidden in plain sight.
Tool poisoning attacks embed malicious instructions inside MCP tool descriptions. When an agent reads the description, it executes the injected command — exfiltrating data, ignoring policies, or taking unauthorized actions. LangSight detects all known patterns automatically.
CI/CD integration
Block merges on
critical findings.
The --ci flag exits with code 1 on any CRITICAL finding. Plug into GitHub Actions, GitLab CI, or any pipeline.
Exit code 0No critical findings — pipeline continuesExit code 1Critical findings — pipeline blocks--format jsonMachine-readable output for SIEM integration--output fileSave results as artifact for audit trail